SOLUTION DRIVEN.
MISSION FOCUSED.
Technology should move your business forward. Ironstack builds and manages IT and security around your goals, your workflows, and your reality.
One Accountable Partner for IT and Security
Ironstack is not a ticket desk and not a tool vendor. We take ownership of your entire technology environment so issues don’t bounce between providers, security gaps don’t get missed, and decisions stay clear. Our role is to prevent problems where possible and step in fast with solutions when they arise.
Security is Built In, Not Added Later.
Every solution we deliver is built with a security-first mindset. No matter which service you use, your systems pass through our security team to ensure risks are identified, monitored, and addressed as part of normal operations, not after something goes wrong.
TECHNOLOGY SOLUTIONS
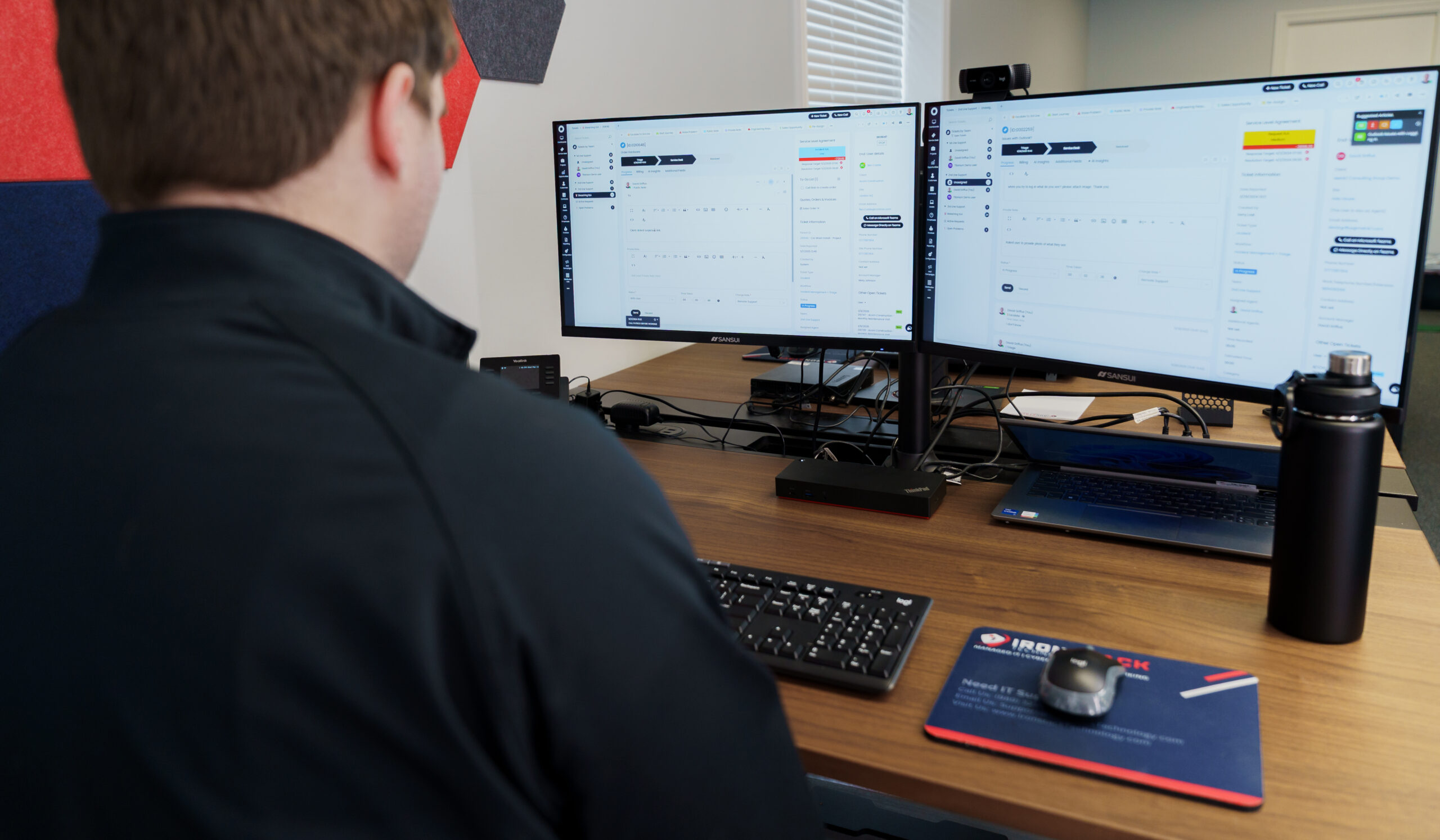
Our Managed IT Services
Solutions working together as one system to support your business
Managed IT
Managed IT Services provide proactive support and comprehensive solutions tailored to your business needs. With 24/7 monitoring, expert support, and strategic planning, we ensure your technology runs smoothly and securely.
Cybersecurity
Our Cybersecurity Services safeguard your business against evolving threats with cutting-edge protection and proactive monitoring. We offer comprehensive risk assessments, real-time threat detection, and incident response to ensure your data and systems remain secure.
Secure Cloud
Our Cloud Services empower your business with scalable, secure, and efficient solutions tailored to your unique needs. From cloud storage and computing to migration and management, we ensure seamless integration and optimal performance.
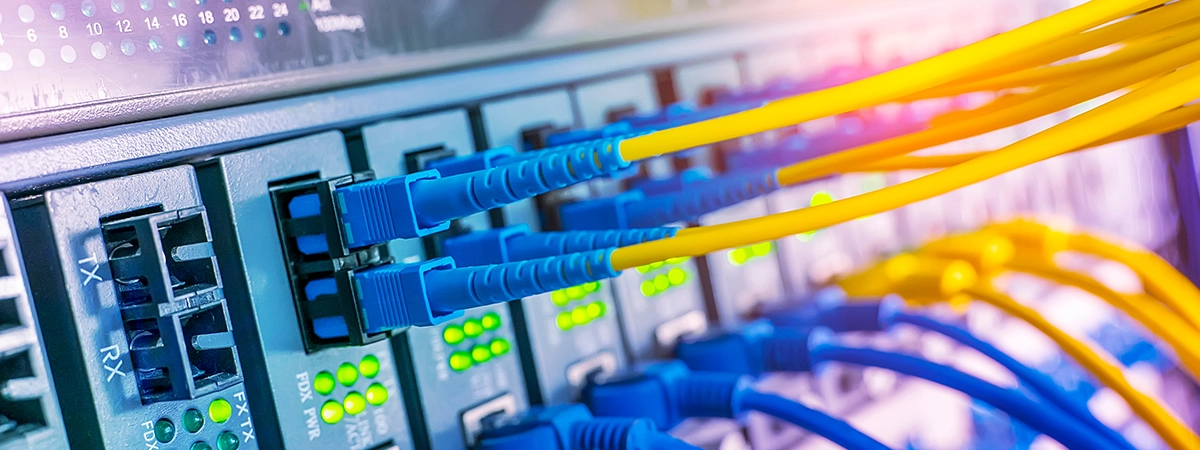
Networking
Our Networking and Connectivity solutions provide reliable, high-speed connections that keep your business running smoothly. We design and implement tailored network infrastructures, ensuring optimal performance and security for your operations.
Business Internet
Our Business and Enterprise Internet solution delivers lightning-fast, highly reliable internet connectivity designed for the demands of modern businesses. Backed by enterprise-grade security, proactive monitoring, and 24/7 support, ensuring seamless operations.
Business Phone
Our VoIP and Collaboration solutions transform the way your team communicates and collaborates, providing crystal-clear voice services and integrated tools. Enjoy seamless connectivity across devices with features like video conferencing, instant messaging, and file sharing.
Microsoft 365
AI Enablement
AI isn’t just a buzzword—it’s a growth engine. Our AI Enablement Service helps you move from experimentation to execution by identifying high-impact use cases, integrating the right tools, and embedding AI directly into your workflows where it delivers measurable ROI.
Web Design
Our approach goes beyond design. We prioritize speed, security, scalability, and search visibility to ensure your website becomes a powerful business asset. Whether you're launching a new brand or upgrading an existing site, we deliver solutions that position you for growth and long-term success in today’s competitive digital landscape.
Need Something Else?
Can't find what you are looking for? Here at Ironstack we have hundreds of products and services. Tell us what you are looking for and we can help build a solution or refer you to someone who can.
Vendors & Partners